HOW-TO
Monitor Network Security of Your Company Resources

As their procedure becomes clearer, and as new technologies are implemented to avoid malware, we can hope to see new technologies rise out of threatening specialists (and truth be told we have a to-and-fro among Amotate and JPCERT in the most recent week). Along these lines, the best strategy for companies to decrease their risk is to adopt a functioning and layered methodology.
If a company endures, the best response is quick. In these sorts of penetration activities, it is regular for attackers to gain early obtain access and pass through the reach of other criminal companies consistently, which grows the reach, depth, and impact of the influence. This winds up being a great lot like having a house visitor who won’t leave and then welcoming their horrible and more dangerous friends to the group.
The most terrible circumstance for big companies in effective Emotet malware is that they deny access to the environment and demand ransom. The worldwide effect of ransomware is assessed to be in the billions in 2019, so the sooner a company can identify a virus, the better.
While antivirus remains competitive, it isn’t bulletproof. Hence, powerful multi-layered ways to guard incorporate endpoint identification, backup and feedback systems, and network monitoring capacities. If a worker is the victim of a phishing trick, against malware protection is required to help cover the initial malware. Notwithstanding, and if this fails, further developed behavioral methods can assist with identifying this sort of malware.
Notwithstanding the many levels of endpoint security, network visibility, and network security monitoring allow companies to have a deeper understanding of what and – above all – who access the network.
Network visibility enables companies to continually monitor network traffic between the Internet and each other from endpoints. The more inside-and-out, dynamic, and comprehensive the company’s network visibility is, the more probable it is to identify malware before it transforms into a stagnant function or catch sideways movement (a malware spread between PCs).
ExterNetworks Network Security Management Services provides deep network vision and capacity to identify threats, allows security teams to have real-time and precise estimates, and anticipate future threats.
Security Policies for Your Remote Team
Working outside the work environment can prompt unfortunate behavior by your team; Mistakes can simply prompt incredible risks. What’s going on if your remote team could act now – and how might your IT security monitoring policy manage them?
They Visit Sites Without Guaranteeing Them Their Security:
With the appearance of COVID-19, hackers are utilizing an ever-increasing number of criminal attacks, catching the fear and seriousness of each snapshot of injury.
Workers might be aware at work, but at home, they are less careful while clicking on links. Ensure that if their gadget is recognized with malicious software, their business resources might be compromised and might be undermined.
Educate your team on the most ideal approach to approve a connection before clicking on it; set a government policy for managing undisclosed links – if all else fails, mislead in favor of alert. Connect your staff with the IT team for support; a protocol of communication and correspondence with technicians to stay connected with the latest.
They Share Work Gadgets – Or Utilize Personal Work Gadgets:
When teams telecommute, they generally work with their personal gadgets. Regardless of whether it’s absolutely a desktop, it’s still at risk. With the right safety measures this doesn’t have to be an issue, yet many individuals treat their personal gadgets significantly less cautiously than they do their laptops and mobile devices and often allow friends to access it. If they utilize personal gadgets, they are probably going to surf the Internet in risky ways and unsafe to your network.
Yet, since those personal gadgets are connected to your network, it’s significant for them to understand: it’s an ideal time to regard every gadget as though it were an organization gadget.
Build up a clear protocol, with potential control if this protocol isn’t maintained, that nobody will share his gadgets with anybody outside the organization. Ensure you communicate your needs plainly with your team.
Far and away superior, don’t allow your team to utilize their gadgets. If you can distribute organization gadgets, this is the most ideal approach to secure your network resources. You will still require a clear protocol on how you expect that these gadgets should be kept out of the property, however, it will be simpler for your team to separate personal habits and work habits. This is the way into any security policy.
They Are Utilizing Poor Passwords To Access Your Network:
25 per cent of workers utilize the same password for everything, which implies that it is simple to hack. Your organization policy should indicate:
Passwords must be specific to each account, adequately complex and different, and sufficiently long to maintain that complexity.
Consider giving your team access to the password manager as a feature of this policy.
Thusly, regardless of whether their password is taken, the hackers won’t be able to access their accounts.
HOW-TO
How to Make the Perfect Espresso at Home

Brewing a perfect cup of espresso within your home’s comfort demands artistic expertise with scientific precision which involves selecting high-quality ingredients with meticulous care. This comprehensive guide presents nine crucial steps, guiding you to enhance your espresso-making powers from the initial selection of beans to the final, satisfying sip.
1. Choose Fresh and Quality Coffee Beans
The journey to the perfect espresso coffee starts with the selection of beans that are not only fresh but of the highest quality, ideally roasted within the past month to ensure maximum flavor and aroma. The type of bean you select plays a crucial role in the overall taste of your espresso, as different origins and roast levels bring their own unique profiles to the cup. Whether you’re drawn to the bright acidity of African beans or the rich, full-bodied flavors from South America, experimenting with various beans from around the world is key to finding the blend or single origin that matches your taste.
2. Calibrate Your Coffee Grinder
Achieving a uniform and consistent grind is essential for unlocking the full flavor of your coffee beans. To ensure this consistency, a burr grinder is indispensable, as it provides uniform grind particles, unlike the less precise blade grinders. The grind size should be similar to the texture of table salt. This specific fineness is vital for the optimal flow of water through the coffee at the right pace, extracting the rich flavors and aromas.
3. Measure Coffee and Tamp Correctly
For a standard shot, aim for 18–20 grams of coffee, a sweet spot that balances intensity and flavor. Equally important is the art of tamping: distribute the grounds evenly in the portafilter and apply firm, even pressure to tamp. Proper tamping prevents water from finding the path of least resistance and channeling through the coffee unevenly, which can lead to over-extracted or under-extracted areas. This attention to detail ensures each shot of espresso is balanced, rich, and full of the intended flavor nuances.
4. Preheat Your Espresso Machine
Preheating your espresso machine, portafilter, and cup helps in achieving temperature stability. This practice ensures that the coffee doesn’t suffer from sudden temperature drops during extraction, leading to a more consistent and flavorful shot. For those looking to elevate their home coffee experience further, investing in the best dual coffee maker can be a game-changer. This device offers the option to switch between brewing espresso and regular coffee. This versatility caters to a wider range of preferences, making it an ideal addition to any coffee lover’s kitchen collection.
5. Understand Your Machine’s Settings
Understanding your espresso machine’s settings is crucial for crafting a perfect cup of coffee. By adjusting the temperature, pressure, and volume, you can fine-tune the machine to achieve your desired flavor. This level of customization provides you with greater control over the extraction process, enabling you to brew each shot precisely to your taste preferences.
6. Time Your Shots
The timing of your espresso should be 25–30 seconds for a single shot, as this window typically yields the best balance of flavors. If your espresso is pouring too quickly or too slowly, it can indicate the need for adjustments in grind size, tamp pressure, or even the machine’s settings. By paying close attention to the timing, you can tweak your brewing process, ensuring each cup of espresso is as delicious as intended.
7. Froth Milk to Perfection
Start with cold, fresh milk for the best results, and steam it until it reaches the sweet spot of 140–150°F. This temperature range is ideal for creating microfoam with tiny, uniform bubbles, essential for the silky mouthfeel of a top-notch latte or cappuccino. Mastering milk frothing elevates your home barista skills, bringing a professional quality to your espresso creations.
8. Clean Your Equipment Regularly
Regular maintenance of your espresso machine and grinder is essential not only for the longevity of your equipment but also to prevent the buildup of coffee oils and mineral deposits, which can adversely affect flavor. Additionally, ensure your grinder is always free from old grounds, as stale grounds can compromise the taste of your espresso.
9. Experiment and Adjust
The art of espresso is personal and ever-evolving. Experiment with different beans, grind sizes, and brewing parameters. Take notes on what works and what doesn’t, and adjust your process to continuously refine your espresso shots.
Conclusion
Mastering the art of espresso at home is a rewarding journey that transforms each cup into a moment of pleasure. Whether savoring the rich intensity of a solo shot or the smooth complexity of a milk-infused creation, by following these steps, you embrace both the meticulous nature and the creative freedom of espresso making.
HOW-TO
How To Use A Personal Loan For Renovating Your Home

Making changes to your house once in a while or often is both quite common. Home renovation is part of every household by improving your bedroom style, putting in some contemporary woodwork, or introducing a completely eclectic decor theme throughout the house.
Renovating a house is a good expense that gives you satisfaction over a long period. A lot of renovations take place around important family functions, festivals, or celebrations. Also, when you have bought a new home or are looking to renovate the existing one. You don’t want to exhaust your savings. Therefore, the best way is to use a personal loan for home renovation for all these purposes.
A personal loan is an unsecured loan that means you don’t have to put a security against the approved loan, which is the most attractive feature of a personal loan. This makes personal loans convenient for those who are just starting a career and do not have assets to put up as collateral.
These are some points to renovate your home using a personal loan:
A Complete Plan Is Necessary
Whenever you do some work, you have to make a complete plan in renovating your home where many expenses occur. In the same way, when you are renovating your home, you should draw up a complete plan before starting your project. Poor planning and execution waste money and valuable resources. Like the home décor, which costs a lot, you have to plan in such a way that it is under your budget. You should make a list of what is necessary and important to you according to their cost. This will make your project easier to understand, and it is a good idea to allow for unexpected expenses.
Stick To A Budget
This is the next most important thing that everyone should follow. Whenever you spend money, it’s a good idea to know how much we are saving from that purchase, whether it’s simply a meal out or buying something big. Most people don’t think about all the small monthly bills or buy unnecessary things that are not required. When we are planning for a personal loan for home renovation, you should be careful to spend money and tighten your monthly budget. You should stick to a planned budget, which will help you in the monthly EMI of the personal loan.
Compare The Price And Offers
Comparing prices is essential before purchasing because it will help you to find great deals on the same item or similar items at discounted prices. In today’s world, everything is dependent on technology. All the information you want is readily available at your fingertips. This makes our life very easier. Instead of going to shops, you can survey the best prices, offers, and reviews online in all categories before making a purchase that comes under your budget, and you can get everything you need.
Personal Loan EMI calculator is Useful
If you take a personal loan, you need to pay the principal and the interest amount. If you are planning for a personal loan, you should use an Equated Monthly Installment (EMI) calculator to estimate the monthly installment payments. According to the plan you have prepared, you have a good idea of the loan you need. The lender determines the interest rate for a personal loan. The EMI consists of the principal amount of the loan and the interest paid on the personal loan.
After that, only the loan tenure remains, which is the period or duration for which the loan amount is sanctioned. You can adjust the tenure of the loan on the calculator. Personal loans, car loans, education loans have shorter tenures as compared to home loans.
Apply for the Personal Loan
Before you go ahead with your personal loan requirements, ensure to check your eligibility first. For applying for a personal loan, you must be a resident of that country, and you have to be between 21 and 60 years of age with a net monthly income of over Rs 30,000. With a good credit score, the probability of your personal loan for renovating a home is higher. These are some steps that need to follow for applying for a personal loan:
1. Fill Out the Application Form.
First of all, you have to fill the application form. Ensure that you provide accurate personal, employment, and financial details. You will also have to fill in your PAN and Aadhar number to proceed to the next step.
- Select the loan amount
- Submit Required Documents like KYC documents (ID and address proofs), Salary slips, bank statements (past 3 months), employee ID, or business proof
- And at last, receive Your Loan Amount
Conclusion
After the above points, we get to know how to renovate your home using a personal loan. A personal loan is very useful for its no collateral, instant approval, cheaper than a credit card, no prepayment penalty after six months, long tenure, etc.
Also Read: WPIT18.com Login
HOW-TO
How to Record Screen on Laptop

Many times we want to screen record on our laptop but we have no knowledge of how to do it. In this article, we will educate you about the simple steps or even the best screen recorders for Windows 10 you can use to screen record on a Laptop.
So let’s get started:
First, we will be covering the manual processes of how to do screen recording on a laptop and then we may also discuss some of the best screen recording software for Windows.
Let’s cover them one by one.
1. Use Game Bar To Record Your Laptop Screen:
Before covering the steps of how to do it, please note the Game Bar option can only be used if you have Windows 10. If you have a previous version of the Windows Operating System, the Game Bar option won’t work. This option though is very easy and comes with a limitation. With Game Bar, you can record the laptop screen of only one program at a time. It cannot be used to record screens with multiple programs. Let’s see how to do screen recording on a laptop using the Game Bar:
- Launch the program or app which you want to record.
- Press the Windows Logo Key and G simultaneously on your Keyboard.
- Doing so will open a dialogue box asking you to open the Game Bar. Choose Yes, this is a game.
- On the Game Bar, click on the Mic icon to screen record with audio.
- Once done, click on the Record button to start the screen recording.
- When you want to finish recording, simply click on the Stop button.
- Post this press Windows Logo Key and E simultaneously to open the File Explorer.
- Copy the address from the Address bar and then press the Enter key.
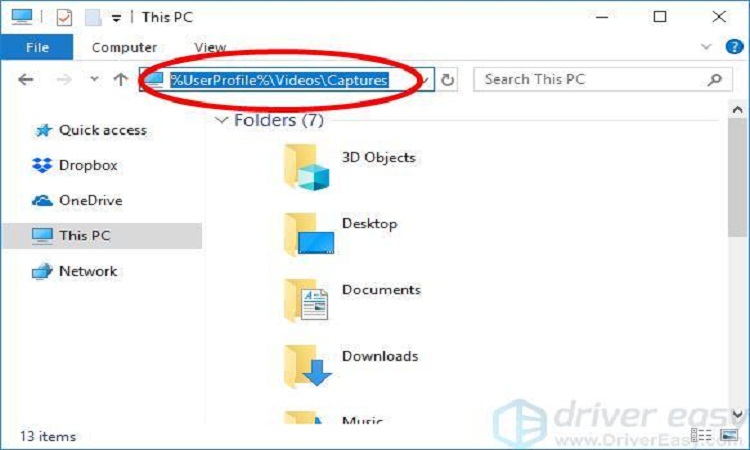
This is how you can record a laptop screen easily using the Game Bar in Windows 10. However, if you do not have Windows 10, and still want to learn how to do screen recording on a laptop, you can also use third-party tools to accomplish the task for you. Let’s see some of the apps to do screen recording on a laptop.
1. ActivePresenter:
ActivePresenter is a third-party screen recorder tool by Atomi Systems that not only records screens but can also be used to edit videos. ActivePresenter is one of the most popular tools to screen record on a laptop and is used by YouTubers, trainers, Faculties, video creators, etc.
ActivePresenter comes in both free and paid versions. The free version itself delivers most of the functionalities and users may want. It lets you capture the screen, trim it, cut, split, make changes in the speed and volume, add animation, etc. Another advantage of the trial version is that it does not add a watermark even in the trial version.
The paid version on the other hand has more advanced features of editing audio and video and also provides software simulations.
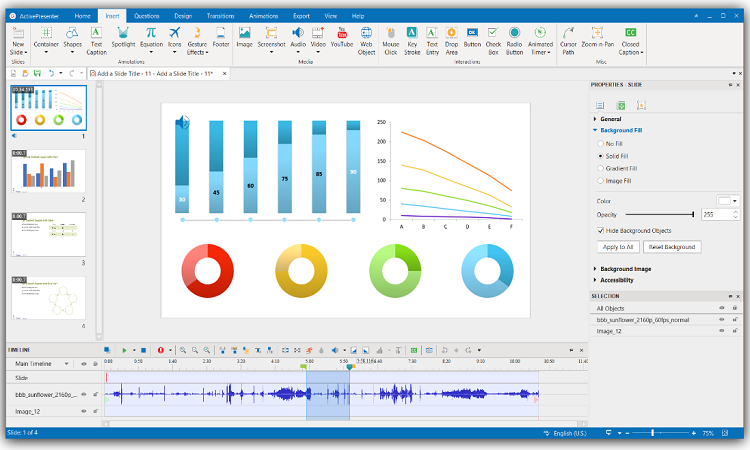
Benefits Of Using ActivePresenter:
- Easily lets you record full screen, a window, region.
- Comes with a video editor that lets you edit captured videos as well as imported videos.
- The free version provides all the basic features like cut, trim, adjust, transitions, animations, change speed and volumes, etc.
- It is ad-free and you can record a laptop screen without any time limit.
- The paid version contains advanced features like the Blur effect, noise reduction, audio fade in/out, etc.
While there are so many benefits of using ActivePresenter to screen records on a laptop screen, it also has some limitations.
- It is available for only 64-bit Operating Systems.
- You cannot schedule screen recording.
- Video cropping features are still missing.
2. OBS Studio:
OBS Studio is another screen recording software that can be beneficial when you are learning how to do screen recording on a laptop. With OBS Studio one can easily screen record, do video recording, and also live stream videos without any watermark and there is no time limit on the duration of the screen recording.
Due to these benefits of OBS Studio software, it is highly recommended for gamers who like to broadcast their gameplay. OBS Studio allows users to capture the entire laptop display as well as capture screen using a webcam or even a microphone which is an amazing feature. It also helps in creating layered videos for webcams and lets the user select the desktop applications as well as the audio sources that they might want to share.
However, OBS Studio does not have a video editor which is still a missing functionality many users look for in a screen recorder application.
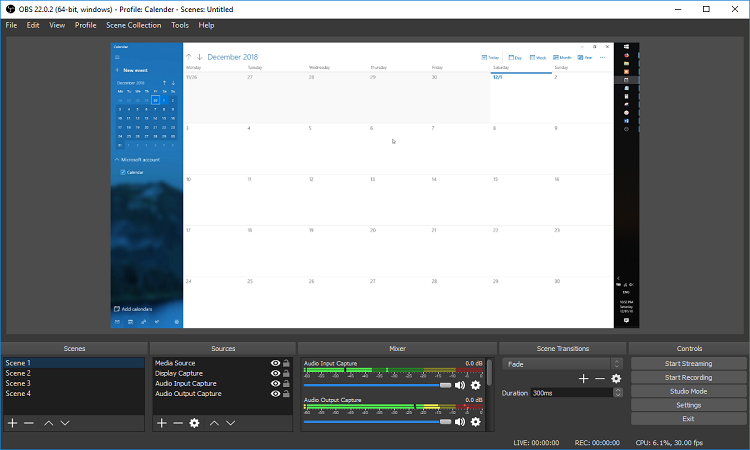
Benefits Of Using OBS Studio:
- Easily lets you record a full screen, microphone, web cam, window, etc.
- It is totally free from any kind of ads.
- Allows streaming to YouTube, DailyMotion, etc.
- It does not contain any watermark.
- Contains all features like cut, trim, adjust, transitions, animations, change speed and volumes, etc.
- Comes with an easy-to-use audio mixer.
While there are so many benefits of using OBS Studio to screen records on a laptop screen, it also has some limitations.
- It does not have a video editor.
- There is no Pause button for recording.
We all might want to record a laptop screen under situations where we might save our work or may need it at a later stage. While you can always take screenshots or write down the steps of the important work, it is always recommended you record the entire screen so that you have it all in one place.
Screen Recorders are also used by gamers to record screens as well as for live streaming. If you have Windows 10 you can easily use the Game Bar option to do screen recording on a laptop. However, since it is only present in Windows 10, others that may have previous versions of Windows can make use of the screen recording tools mentioned above and easily learn how to do screen recording on a laptop.
-

 GAMING3 years ago
GAMING3 years ago5 Coolest Patterns In Mirror Cube That You Should Know
-

 Reviews2 years ago
Reviews2 years ago9xflix Com | 9xflix 2022 Bollywood Movies Download
-

 PC/TABLET/MOBILES4 years ago
PC/TABLET/MOBILES4 years agoPc Builder: Find The Best Parts For Your Pc And Your Workstation
-

 GAMING3 years ago
GAMING3 years ago11 Top Alternatives To Stream2watch For Live Streaming Sports
-

 TECH3 years ago
TECH3 years agoComplete Guide of 1337x Proxy 2021 | List of Unblocked 1337x Sites
-

 TECH3 years ago
TECH3 years agoWhat Are The Tricks To Resolve The Fritzbox 7590 Red Info Light?
-

 APPS AND SOFTWARE3 years ago
APPS AND SOFTWARE3 years agoBuild A White-Label On-Demand Service Marketplace In A Snap With The Thumbtack Clone
-

 PC/TABLET/MOBILES3 years ago
PC/TABLET/MOBILES3 years agoTop 7 Tech Products of the Decade That You Must Know















